The Short Version
If your business handles personal information about Massachusetts residents — employee Social Security numbers, customer financial account data, patient records — state law requires you to have a Written Information Security Program. Full stop.
This applies regardless of your business size. It applies even if you’re headquartered in Texas or California and simply have customers or employees in Massachusetts. It’s been the law since 2010, and the Attorney General has been enforcing it.
A WISP is a formal, written document that describes how your organization protects personal information. It covers who’s responsible for data security, what systems and data you have, how you control access, how you train employees, how you manage vendors, and what you do when something goes wrong.
The good news: creating a WISP is not complicated. The document itself can be written in a few hours with the right structure. The harder part — which most small businesses skip — is actually operating the way the document says you will.
This post walks through exactly what the law requires, what each section of a WISP should contain, and what the Attorney General actually looks for when investigating a breach. At the bottom of this page, you can build your own customized WISP for free using our interactive generator.
What the Law Actually Says
Massachusetts 201 CMR 17.00 — officially called the “Standards for the Protection of Personal Information of Residents of the Commonwealth” — was enacted in 2010 and updated in 2019. It is one of the most specific state data security regulations in the country.
Who it applies to. Any individual, company, or other legal entity that owns or licenses personal information about Massachusetts residents. There is no revenue threshold, no employee count minimum, no industry carve-out. A two-person accounting firm, a 50-person staffing agency, a multistate retailer with a handful of Massachusetts customers — all covered.
What counts as “personal information.” Under MA law, personal information means a Massachusetts resident’s first name (or first initial) and last name, combined with any of the following:
- Social Security number
- Driver’s license number or state-issued ID number
- Financial account number (checking, savings)
- Credit or debit card number — with or without any security code or password that would allow access
If you only have a customer’s name and email address, that combination does not trigger the regulation. Once you add a financial account number or SSN to that record, it does. This distinction matters for scoping what your WISP needs to cover.
The 2019 update. A 2019 amendment to MGL c. 93H added a specific WISP requirement to breach notifications. If your business suffers a breach and must notify the Attorney General, your notification must now state whether you have a WISP and what actions you took under it. If you don’t have one, that fact is now on record with the AG’s office. It tends to affect how seriously an investigation proceeds.
Penalties. The AG can bring enforcement actions under MGL c. 93H and c. 93A. Civil penalties run up to $5,000 per violation. In breach situations, each affected individual can be treated as a separate violation. Costs compound quickly, and that’s before you account for legal fees, mandatory credit monitoring, and reputational damage.
What Goes in a WISP, Section by Section
The regulation specifies components a WISP must address. Here is each one, what it means in plain terms, and what it looks like in practice for a typical small business.
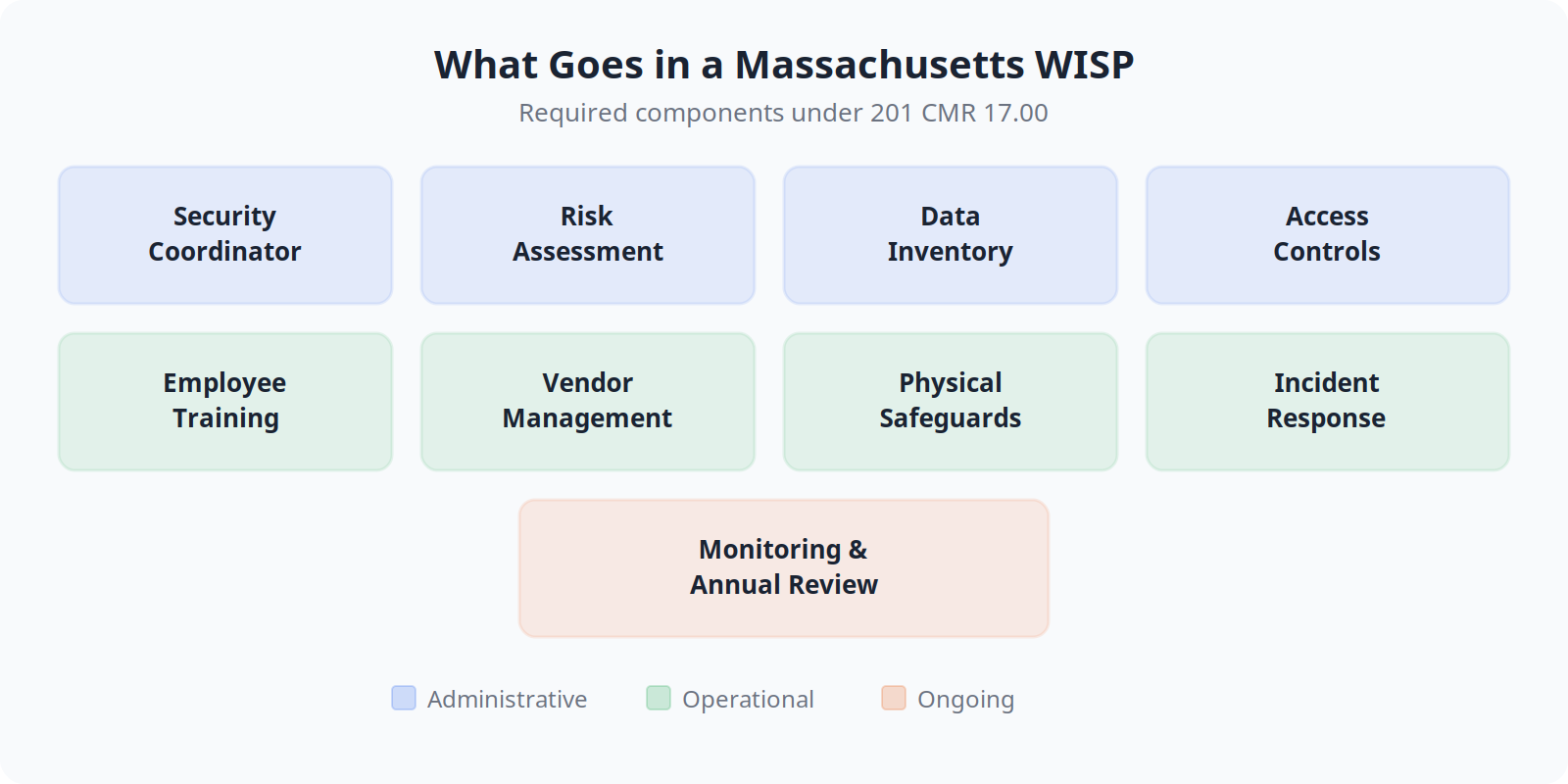
Designated Security Coordinator
The regulation requires you to identify a person responsible for your WISP.
In practice: For a 20-person company, this is usually the owner, office manager, or an outsourced IT provider. The name and title should appear in the document, along with what their responsibilities are (conducting the annual review, overseeing incident response, etc.).
Common mistake: Listing a role without naming a person, or listing someone who has never seen the WISP. If the AG asks who runs your security program and that person can’t speak to it, the document loses credibility immediately.
Risk Assessment
You are required to identify and assess reasonably foreseeable risks to the security of personal information, in each relevant area of your business.
In practice: This means looking at three categories: employee handling and training, physical security of records and devices, and your technology systems. A written risk assessment does not need to be a 40-page document. It can be a structured narrative or a table. What matters is that it reflects your actual business — the kinds of data you have, where it lives, and where breaches are most likely to happen.
Common mistake: Skipping this entirely and jumping straight to controls. A WISP without an underlying risk assessment has no logical foundation and it shows during an investigation.
Data Inventory
You need to know what personal information you have, where it is, and how it flows through your business.
In practice: For a small business, this is often simpler than it sounds. It means documenting that employee W-2 data lives in your payroll system, that customer credit card data flows through your POS and gets tokenized, that paper files with SSNs are in the locked cabinet in the back office. The inventory does not need to be exhaustive on day one, but it needs to reflect reality.
Common mistake: Forgetting shadow data — the spreadsheet someone built years ago that has client account numbers, the HR folder on the shared drive with scanned I-9 forms. Data inventories tend to uncover more than businesses expect.
Access Controls
The regulation requires limiting access to personal information to those who need it to do their jobs, and having procedures for granting, changing, and revoking access.
In practice: This means role-based access controls in your systems, a process for removing access when an employee leaves, and a prohibition on sharing credentials. For most small businesses, implementing this is more of an IT configuration task than a policy writing task. Your WISP documents what the controls are and who’s responsible for maintaining them.
Common mistake: Having no offboarding process. Ex-employee accounts left active after termination are among the most common findings in breach investigations.
Employee Training
Employees who handle personal information must be trained on your WISP and on their security responsibilities.
In practice: Annual training is the standard. It does not need to be a full security awareness platform. At minimum: a review of your WISP, discussion of phishing and social engineering, rules around handling personal information (don’t email SSNs, don’t use personal devices for work data), and what to do if something goes wrong. Keep a record that training happened.
Common mistake: Listing “annual training” in the WISP but never actually conducting it. This is the single easiest thing for an investigator to verify by asking employees directly.
Vendor Management
If you share personal information with third-party vendors — payroll processors, cloud storage providers, IT support — you are required to ensure those vendors maintain appropriate protections and to have written agreements with them.
In practice: This means your contracts with vendors who touch personal information should include security provisions. Most reputable cloud vendors (AWS, Microsoft, Intuit) will sign data processing agreements on request. Your WISP should describe how you evaluate vendors and what your contractual requirements are.
Common mistake: Using a vendor for years without ever asking about their security practices or having any written agreement that addresses data protection.
Physical Safeguards
Personal information stored or handled in physical form — paper files, printed reports, portable devices — requires physical controls.
In practice: Locked filing cabinets for sensitive paper documents, clean desk policies, secure disposal (shredding, not recycling bins), and policies around laptops and USB drives leaving the office.
Common mistake: The laptop policy. Unencrypted laptops are the most common vector in MA breach notifications. If a device with unencrypted personal information is lost or stolen, notification is almost always required. Full-disk encryption is not expensive and it eliminates this exposure.
Incident Response
Your WISP must include a plan for responding to security incidents — what you do when something goes wrong.
In practice: This section should name who gets called, in what order, what the first steps are (contain the incident, assess the scope, determine notification obligations), and who handles communication. For small businesses, this can be a single page. The goal is that when something happens at 7 PM on a Friday, your team isn’t starting from scratch.
Common mistake: Having no plan. Businesses that reach the AG’s office after a breach without a documented response plan are in a significantly worse position than those who can show they had a procedure and followed it.
Monitoring and Annual Review
The WISP is not a one-time document. The regulation requires periodic reviews and updates, especially after a security incident or material change in operations.
In practice: Schedule an annual review. Check whether the risk landscape has changed, whether your data inventory is still accurate, whether there have been any vendor changes, whether training has been completed. Document that the review happened and what (if anything) changed.
Common mistake: Publishing a WISP in 2021 and never touching it again. An outdated WISP that doesn’t reflect your current operations is worse than a simple, current one.
The Hard Part: Enforcement
Here is the honest version of this conversation.
Writing a WISP takes an afternoon. Getting it right takes a few more hours. Getting it printed, signed, and filed — easy.
The hard part is operating the way the document says you will, every day, for years.
Annual training that actually gets scheduled and documented. Access reviews that happen when employees leave and not just when someone thinks to do it. Vendor agreements that get reviewed when you bring on a new cloud tool. Encryption deployed on every laptop before someone takes one to a coffee shop.
When the Attorney General’s office investigates a breach, they do not grade you on the quality of your WISP document. They ask for the WISP, and then they start checking whether you were following it. They ask employees about training. They ask for records of your last risk assessment. They ask for evidence of your incident response. They ask which vendors you’ve audited recently.
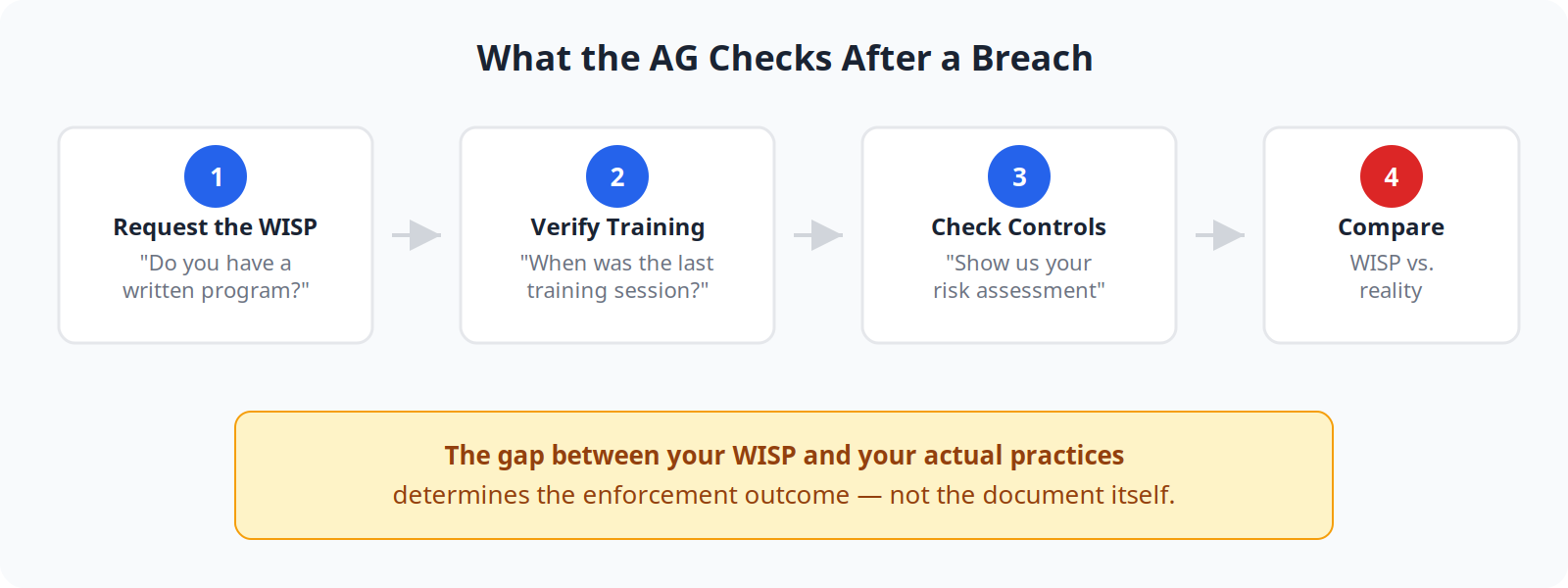
Businesses that had a good-faith, operational security program — even an imperfect one — are treated very differently from businesses that had a document they filed once and forgot.
Most small businesses get the document part right. Most small businesses struggle with the operational part. Not because they don’t care, but because security programs require consistent attention from someone who owns the work, and in a 15- or 20-person company, that person usually has three other jobs.
That’s the gap where outside help typically earns its value. Not writing the document — that’s what this page is for. Making sure the program actually runs.
Real Enforcement: What Happens When the AG Comes Knocking
The Massachusetts AG’s office publishes an annual Data Breach Report with enforcement trends and case summaries. Several patterns appear consistently across small business investigations.
The unencrypted laptop. A small professional services firm reported a stolen laptop containing client financial records — names, account numbers, SSNs. The firm had no full-disk encryption policy and no mention of encryption in their WISP. Result: notification to over 1,000 individuals, AG investigation, consent agreement requiring encryption deployment across all devices and a WISP rewrite within 90 days.
Lesson: Encryption is the single fastest way to remove the most common breach vector. A lost or stolen encrypted laptop typically does not trigger notification obligations. An unencrypted one almost always does.
The healthcare practice with no incident response. A small medical practice experienced a ransomware attack. Patient records — including names, insurance numbers, and SSNs — were encrypted by the attacker. The practice had a WISP but no incident response plan. They waited two weeks before notifying patients while trying to recover data on their own. Under MGL c. 93H, notification must occur “in the most expedient time possible.” The delay, combined with the absence of an incident response procedure, factored into the enforcement outcome.
Lesson: The incident response section of your WISP needs to include notification timelines. MA law does not have a fixed 72-hour window like GDPR, but “expedient” is interpreted strictly. Know before an incident who decides when to notify and how quickly.
The WISP that was never followed. A mid-sized company in a regulated industry had a detailed, professionally written WISP. Employee training was listed as an annual requirement. Access controls were described in detail. Vendor management language was thorough.
After a breach, the AG’s investigation found that training had not occurred in three years, a former employee’s access credentials were still active, and the company could not produce a vendor data processing agreement for the third-party tool where the breach originated.
The existence of a well-written WISP made the enforcement outcome worse, not better — because the document created an expectation the company demonstrably hadn’t met.
Lesson: A WISP you aren’t following is a liability document, not a protection. If you create one, plan to operate it.
Build Your WISP — Free
Answer a few questions about your business and get a complete, customized WISP as a .docx file — ready to sign and put in front of your team. Takes about 5 minutes. Free. No account required.
The generator will identify gaps in your current security posture and flag specific areas where your WISP needs attention, all based on the actual requirements of 201 CMR 17.00.
Open the WISP Generator in a new tab →
Nicholas Salem is the CEO of Boston Managed IT, a managed services provider serving professional services firms and small businesses across Greater Boston. BMIT helps clients build and operate security programs that meet Massachusetts compliance requirements.